This is the second in what I’m hoping will be a series of a few posts focusing on improving your digital security and privacy – it’s something that’s in the news a lot right now and will only grow more important. Hopefully, you’re here because you’re one of those people who wants to know what steps they can take to improve their security and/or privacy online. This post is going to focus on VPNs – how they work, what they can (and cannot) do and what you should consider when picking one. It’s aimed at people who aren’t security or networking experts.
Summary
If you’re only vaguely interested in improving your security or privacy without the detail and the reasoning, here’s the summary:
- VPNs arent magic privacy saviours that suddenly make you impossible to track.
- They can help in some situations – if you don’t trust the network connection you’re on in a shop or cafe, if you want to make a specific effort to hide your activity from your ISP (Internet Service Provider like BT, Virgin Media, AT&T)
- Never use a free VPN – their business model often involves selling your data and making things you’re trying to avoid even worse. If you’re in a rush to pick one, use Mullvad. If you are considering paying for access to a wider suite of privacy preserving tools like encrypted email, try ProtonVPN.
Read on if you’d like more of an in-depth understanding of why these things matter and how to understand enough about it to make these choices for yourself.
Intro to the internet
To understand more about how VPNs can help, you need to understand a little bit about how the internet works, but only at a high level. At its simplest, when you type in “www.google.com” into your browser, your computer doesn’t immediately connect directly to Google. Your internet traffic follows a winding path, first to servers owned by your own ISP, then on to their ISP, and so on until it eventually reaches Google. There could be tens of “hops” between your computer and Google, like this:
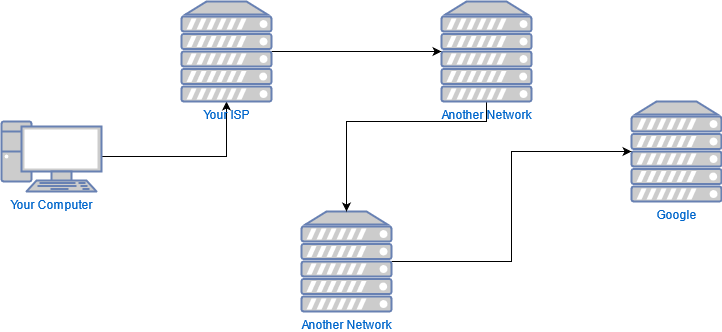
This very first hop between your device and the ISP can be thought of as the “riskiest” because its the easiest one for a malicious attacker to interfere with or snoop on (like setting up a dodgy WiFi hotspot in a cafe).
Let’s now consider the example above but introduce a VPN into the mix.
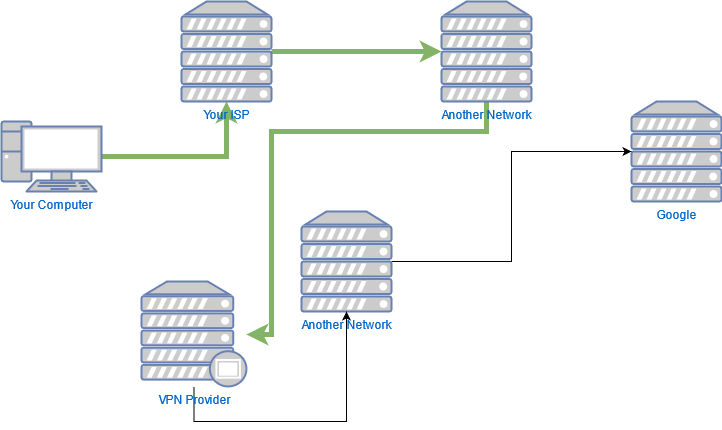
The thick green arrow represents traffic flowing through your VPN through whats commonly known as a “tunnel”. This traffic is completely encrypted such that your ISP and the other networks it flows through can see nothing about it, except that it’s going to your VPN provider. From your VPN provider, it still needs to flow through other networks to your destination – but by that point your tunnel has finished, so its now just normal traffic again like it was in the first example.
In other words, it’s provided you with some protection on the first untrusted network, and hidden some of your activity from your ISP, but you’re not really hiding anything from Google (other than where you first came from) since all you’ve done is taken a different road there. Think of a VPN as like taking a different road to avoid a dodgy area rather than putting on a full disguise before you set off, like they’re often marketed as.
UK Internet Connection Records
You’ve probably never considered the fact that you maybe shouldn’t trust your own ISP before, but I’d like to take a quick detour to give a real-world example as to why you might not. In short, the UK government introduced legislation a few years ago that could require ISPs to store records of your browsing history and online activity for 12 months – and they’re now beginning to test the practical rollout of this capability. These so-called Internet Connection Records (ICRs) are essentially metadata about where you go, what you do and when you do it. I’d encourage you to read the full Wired article about the activity, but the gist is that soon your ISP may well be collecting logs tracking everything you do online. This is ostensibly a law enforcement power but in reality there will be nothing to stop ISPs monetising these records for targeted advertising or criminals stealing the records and using them for blackmail. As you can hopefully now visualise, using a VPN that terminates outside of the UK can help to hide the details of your browsing activity from your ISP if you desire – but making a bad choice of VPN provider can have a substantially more negative impact on your security so its important to understand the choice you’re making.
What can VPNs do
We’ve already hinted at a few of the reasons you might want to use a VPN, but for clarity the main benefits you can get from them are:
- Making yourself appear to websites as if you’re coming from a different location. This could let you access streaming or web content only available in some countries, and it works by tunneling your traffic through a tunnel that pops up in a different country to the one you’re actually in.
- In a similar vein, you can use them to hide the IP address you’re really coming from – websites will see you as coming from the VPN provider’s servers and your traffic will be mixed in with all the VPN provider’s traffic, making you very slightly more difficult to track online in some situations.
- Encrypting your traffic through an untrusted network, whether that’s because you don’t trust the cafe WiFi you’re connected to or you don’t trust your ISP itself. More and more websites and apps these days are using HTTPS, which commonly gets talked about as being “the green padlock” in the browser’s address bar. This means that your traffic is encrypted – but only the data you’re sending back and forth: the destination can still be seen. A VPN can hide all of that from prying eyes – they’ll only see the tunnel to the VPN provider, but nothing about what’s happening inside. It’s important to remember this protection only goes as far as the tunnel – when it hits your VPN provider’s servers, you’re unceremoniously spat back out as normal internet traffic once again.
What can VPNs not do
I’d also like to tackle a few misconceptions about VPNs and clarify what they cannot do, despite some marketing hype.
- They do not protect you from malware and viruses. Whilst there are a couple of VPNs that introduce technology that can help a little, the vast majority aren’t going to have really any impact on this. Your browsing behaviour (by which I mean good “cyber-hygiene” like having good passwords or not visiting dodgy websites) is a much more important factor.
- They do not make you impossible to track or invisible online. All you’ve done is taken a different route to the website – you haven’t arrived in an elaborate disguise.
What to look for when picking a VPN
As is hopefully clear by now, it’s really important to pick a legit, trustworthy VPN vendor because you’re entrusting them with the safe transport of your traffic. For sites that don’t use HTTPS (no green padlock), your VPN provider can see everything you do and send online and for those which do use HTTPS, they can still track what sites you visit, just not necessarily what you do while you’re on them. Here’s a few tips for what to look for when you’re choosing a VPN:
- Avoid free VPNs. Running a VPN service is not free – a provider needs to run servers and pay for bandwidth so often free VPNs are monetising your data whilst claiming to improve your privacy. There can be exceptions to this – ProtonVPN is one of my recommended picks and comes with a basic free tier, but it still has the same privacy commitments.
- Look for a provider that offers third-party audits or security reviews to confirm their assertions of what they do to preserve your privacy and security. This illustrates a commitment to finding and resolving potential security issues. A provider who doesn’t offer these is essentially saying “just trust us” when you ask about privacy or security – and you shouldn’t settle for that. Don’t feel you necessarily have to be able to understand these reports which are often deeply technical – their existence can be enough.
- Another feature to look out for is that the provider keeps no logs. Not keeping logs of your usage of the VPN means there’s nothing to be handed over to law enforcement or hacked and potentially used to blackmail you. Related to the previous point, this is often covered as part of an audit.
- On a more practical note, make sure that a provider has apps for all of the devices that you use. A VPN that only supports Windows and Android is of limited use to you if you mainly use an iPad whilst travelling for example. Make sure you find one that can work for you in all the scenarios you may need it.
- The country where a VPN provider is based is surprisingly important because legislation on data privacy and law enforcement data access can affect the customers of a VPN. A provider based in a country with strong legal protections around data and online privacy is a better choice than a country where the government can wield enough power to impose logging requirements or wiretap type interventions.
Recommendations
There are plenty of VPNs out there that are available from legitimate vendors that do take privacy and security seriously, and have all the things that I’ve discussed above. If you’re in a rush and want to make sure you pick a good one, consider either of these two providers.
Mullvad
Mullvad is a VPN provider that requires no personal information to open an account with, and allows you to pay totally anonymously if you choose. They’re based in Sweden, publish regular audits, keep no logs and are reasonably priced. Mozilla, the makers of Firefox and a company well known for their commitment to online privacy uses Mullvad to power Mozilla VPN.
ProtonVPN
Proton is a Swiss company who offer a variety of security and privacy focused services, like fully encrypted email services, alongside a VPN offering. They also commit to no logging and have published audits of all their apps. They’re slightly more expensive than Mullvad but if you’re interested in their encrypted mail service as well, you can bundle them together for a small discount.

You must be logged in to post a comment.